2023 - The Year of the Cyber PeterEnersec delves into the future of 2023 and looks back at the previous year to see what lessons can be identified.
Data breaches, ransomware attacks, and crypto-currency pyramid scheme collapses dominated the headlines in 2022. The crystal ball predicts that this will continue into 2023, coupled with worldwide recession, stock market collapse, wars, impending global climate disaster, semiconductor supply chain issues, famine and plague. Oh, and let's not forget inflation, the cost of living crisis and potholes in the road. More on those pesky potholes later.
Is there any good news? Yes indeed the opportunities for the global cybersecurity experts (heroes) to come riding to the rescue are many. However before we delve into those opportunities, we must first look at the Peter Principle. The what!? I hear you cry.
The Peter principle is a satirical theory developed by Laurence J. Peter, who postulates that people in a hierarchy rise to "a level of respective incompetence", until they reach a level at which they are no longer competent.
This is standard practice in politics. UK Politicians and Prime Ministers are a case in point.
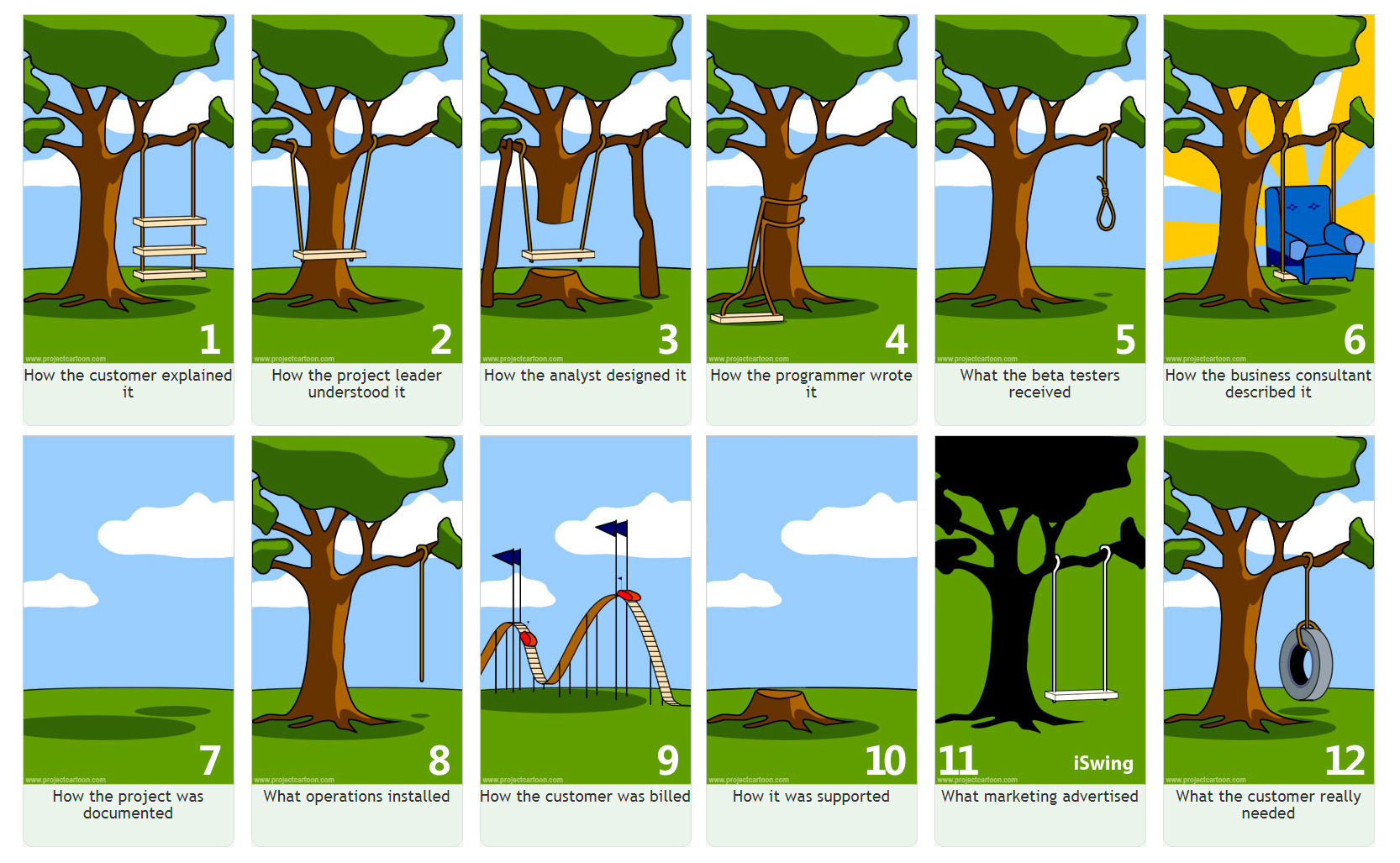
The principle has been adopted by the software community known as the Software Peter principle, which describes a faltering project which has become too complex to be understood even by its own developers.
Now this sounds familiar.
In 2023 we will see the rise of the Cyber Peter principle. The entire cybersecurity ecosystem has become so complicated and convoluted, that people, organisations and entire governments no longer know which way is up.
Lets face it, those in perceived control at their relative incompetency level are too busy checking out the latest social media news and gossip, which will influence their next misguided political or business move.
Shadow IT devices in 2023 will reach epidemic proportions, the warnings have been coming for some time. Shadow Apps and processes that emerge in government and the private sector are due to lack of oversight. IT departments do not provide the staff with the tools to do the job, or at least do the job easily. Security is deemed too difficult to comply with no matter how many staff training seminars are conducted.
Social Media apps will continue to be a prime source of social engineering in 2023. Reliance upon social media, verging on addiction does not help control the prime resource of social engineering and cyber attacks. Time and time again social media is used to trick, coerce and gain access to bank accounts and in some cases entire IT systems. The media industry is in itself addicted to social media. This is a self fulfilling prophecy akin to Stockholm Syndrome, using promoting and defending the very thing they hate most, misinformation and disinformation platforms.
Cabinet ministers conduct government business via whatsapp on personnel phones, because official alternatives are too difficult, inconvenient and cumbersome. Humans take the easy route everytime. If there are no consequences for breaking rules, then rules will be broken.
Cybersecurity marketing brochures and policies for robust cybersecurity do not meet the real people at the coalface.
The tools to do the job quickly and efficiently and securely must be provided to the workforce, otherwise insecure workarounds and alternatives will be found and used, and this starts at the top and trickles down.
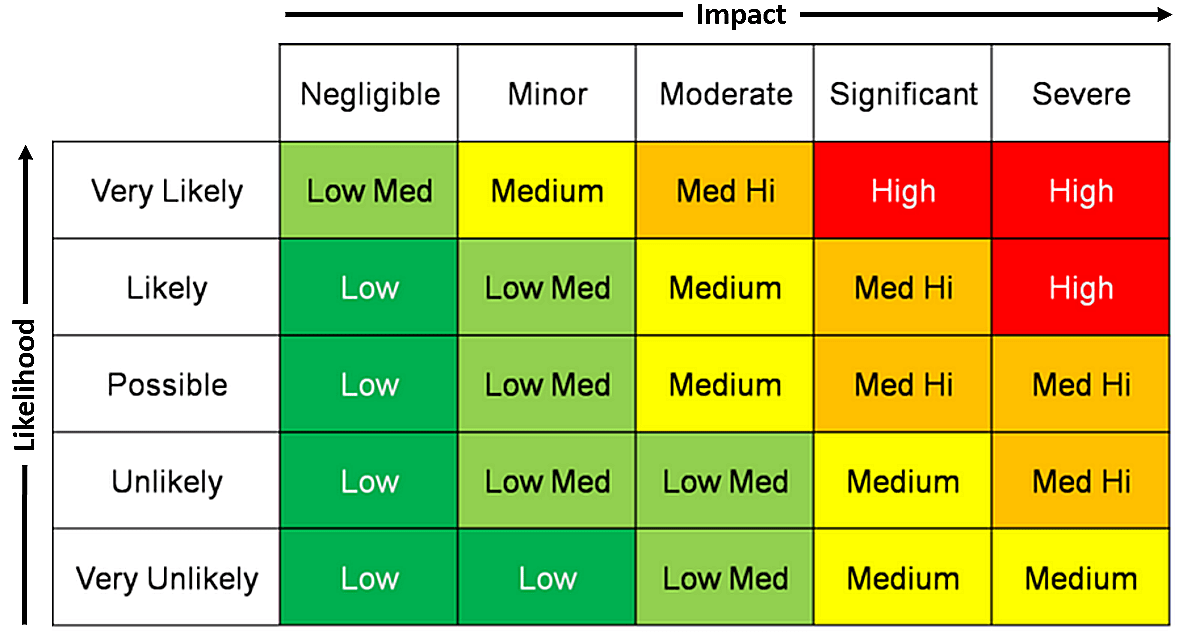
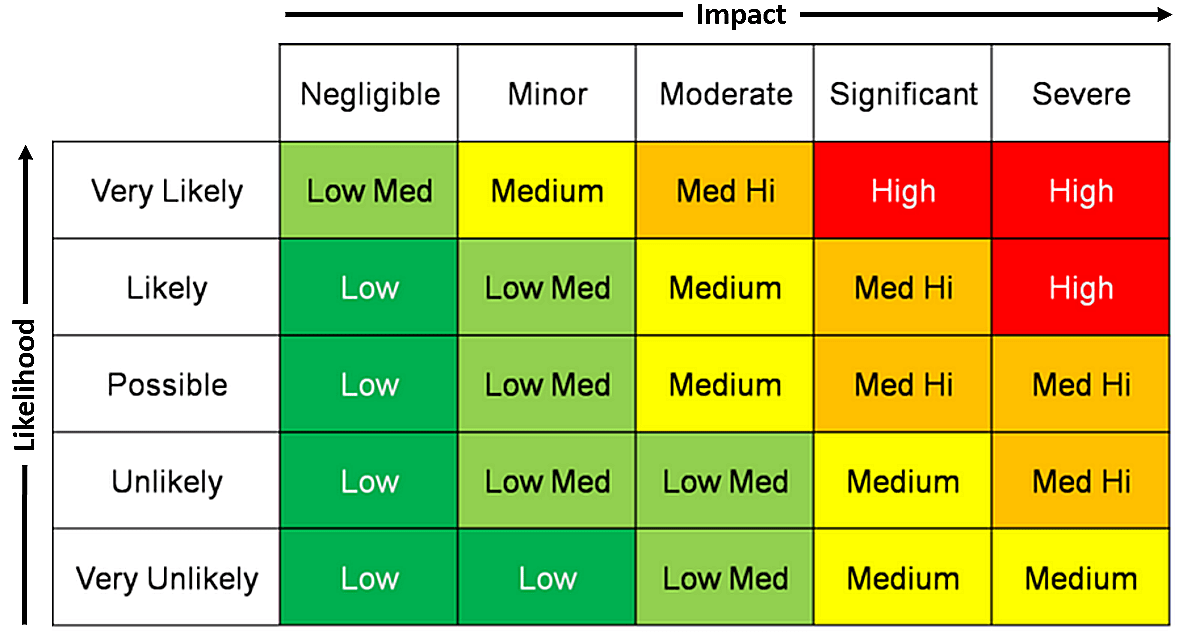
The foundation stones of cybersecurity are beyond the scope of most IT departments. The operating systems and microprocessors that we all rely on are not perfect, far from it. All IT departments can do is to patch quickly and anticipate obsolescence, with a future proof plan of action. Understand the risks and mitigate them.
This brings us back to those pesky potholes, “4000 holes in Blackburn, Lancashire.” Over the years I have noticed across the UK that the state of the roads has noticeably deteriorated. The potholes appearing, which are not being fixed, have reached epidemic proportions. In my local area after the 2022 pre-Christmas freeze and thaw, many new holes have appeared. I don’t expect that they will be fixed anytime soon. We have the technology to get people to the moon, and yet fixing potholes quickly seems beyond us.
What have potholes got to do with cybersecurity?
If councils cannot fix potholes in the road, they cannot fix cybersecurity holes. The state of a nation's roads are a direct reflection on its governance.
Let's imagine a different approach. Prevention is better than cure. Repair cracks before they get worse. Use AI and available data to proactively monitor for holes. Repair holes asap, with repair drones, to avoid further consequences. Invest in new road surface technology and drainage. Think 10-20 years in advance.
Policies are easy - Free school meals for all children. Making this happen is another matter.
Businesses and governments that will succeed in 2023 are those that understand the cyber risks they carry. Those that can revert back to a pen and paper strategy in the case of a cyber meltdown, whilst the systems are being repaired from the backup, to enable the business to function, will prosper. Technology is not the silver bullet that it has become in many organisations. Flights cancelled due to IT disruption? Give me a break. Have you tested your DR plan? No of course you haven’t as this is too disruptive. It’s working, don't touch it, is the cry from all those senior executives, on final salary pensions with only one year to go. Then it will be someone else's problem.
Do senior executives understand their PKI infrastructure, or reliance on unencrypted removable media processes? Do they realise that their IT department has introduced backdoor processes to enable them to do their job, whilst appearing to adhere to cybersecurity policy?
When a company is hacked, and data breached, we get an initial news report and then all goes quiet. The root cause analysis is not public, nor is the fact that millions were paid to the criminal ransomware hackers, to get the crypto-keys, which never appeared. The exploitation of the vulnerabilities that were discovered during the cyber essentials audit, went unfixed. No consequences.
Integrity will be a big word in 2023. We only need to look at The Post Office Horizon IT Scandal to see the worst of it. Little old ladies sent to prison and lives ruined. Again no consequences for those in charge at the time.
The cybersecurity industry badly needs clear lines of responsibility and consequences for breaches that impact lives. We require transparency and accountability. This starts with an audit of your cybersecurity and a plan.
Let's look at those opportunities. Go back to basics, ask your IT department for a firmware audit, this will keep them busy for a while as like in every organisation this foundational cornerstone is very often neglected. Test your DR plan. Check your source code is signed and integrity checked. Are your private keys really private? Ask your IT department for proof and to place that evidence in the evidence folder. Is your evidence admissible in court? If you are called into court could you state that you did everything you could have done, to prevent the cyber attack that cost lives or livelihoods.
I expect in the future, possibly in 2023 that a CEO will not be able to answer yes confidently and will be found guilty of negligence and will end up in prison, where they belong.
Keep your hands on the wheel and eyes upon the road, and don't forget to rock n roll.
Good luck for 2023.